LinkedIn account security in 2026: Protect and scale outreach

LinkedIn faces unprecedented security challenges in 2026, with the platform having uncovered over 86 million fake profiles in just six months during 2024. Digital marketing agencies and sales professionals managing multiple accounts for client outreach encounter escalating risks from account takeovers, phishing attacks, and automation bans that can devastate lead generation campaigns. This guide delivers actionable security protocols, compliance strategies, and verified account advantages to protect your LinkedIn assets while scaling outreach safely and sustainably.
Introduction to LinkedIn security threats in 2026
The LinkedIn security landscape continues evolving rapidly as attackers develop sophisticated methods to compromise accounts and exploit platform trust. The massive presence of fake profiles demonstrates how threat actors create deceptive networks to conduct phishing campaigns, harvest data, and damage legitimate business operations. For agencies managing client accounts, these threats multiply exponentially because a single compromised profile can cascade into broader security incidents affecting multiple stakeholders.
Account takeover attempts surge as automated bots scan for vulnerable credentials and weak authentication protocols. Sales professionals face particular risk when using shared devices or public networks without proper IP management and session controls. Recent data breaches affecting major platforms have heightened LinkedIn's security measures, resulting in more aggressive detection algorithms that can mistakenly flag legitimate outreach activities as suspicious behavior.
These risks uniquely impact agencies because:
- Multiple team members accessing client accounts create authentication complexity
- High-volume outreach campaigns trigger automated detection systems
- Shared IP addresses and devices raise red flags for LinkedIn's security algorithms
- Client data protection obligations multiply compliance requirements
Agencies must adopt safe LinkedIn account management protocols that balance security with operational efficiency. Proactive, layered defenses become essential rather than optional, requiring technical controls combined with staff training and continuous monitoring. The cost of reactive security far exceeds preventive investments when account bans disrupt revenue-generating campaigns and damage client relationships.
LinkedIn policies and regulatory environment
LinkedIn's User Agreement establishes strict boundaries around automation, account sharing, and data usage that agencies must navigate carefully to maintain account standing. The platform enforces limits on automation and requires users to engage authentically without employing deceptive practices or violating member privacy. Understanding these policies prevents inadvertent violations that result in permanent account restrictions or legal exposure.
Specific automation action limits matter because LinkedIn's algorithms detect patterns inconsistent with human behavior. Connection requests, profile views, messages, and endorsements all carry daily thresholds that vary based on account age, activity history, and trust signals. Exceeding these limits triggers escalating consequences from temporary restrictions to permanent bans, making compliance monitoring essential for sustained outreach success.
GDPR and CCPA impose legal obligations on how agencies collect, store, and process prospect data obtained through LinkedIn. These regulations mandate transparent data practices, explicit consent for communications, secure storage protocols, and prompt breach notifications. Non-compliance carries severe financial penalties and reputational damage that can devastate agency operations and client trust.
Consequences of non-compliance include:
- Immediate account suspensions disrupting active campaigns
- Legal liability under privacy regulations with fines up to 4% of annual revenue
- Loss of client contracts due to security incidents
- Permanent platform bans preventing future LinkedIn usage
Aligning security practices with evolving platform standards requires ongoing attention to LinkedIn's policy updates and regulatory changes. Agencies must implement safe LinkedIn account management frameworks that embed compliance into daily workflows rather than treating it as an afterthought. This proactive approach protects both operational continuity and legal standing in competitive markets.
Best practices for LinkedIn account security
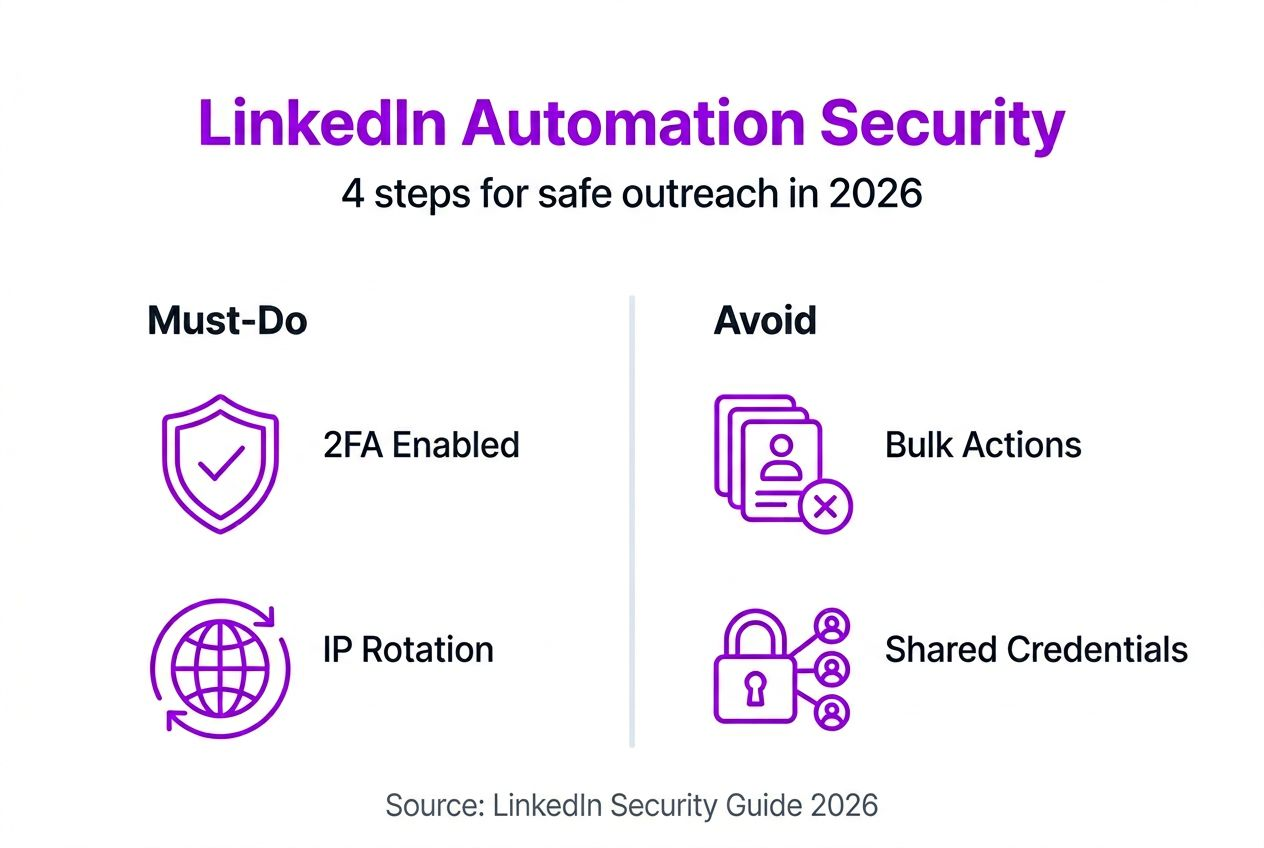
Technical security measures form the foundation of account protection, starting with mandatory two-factor authentication across all LinkedIn profiles and associated email accounts. Two-factor authentication blocks 99.9% of automated takeover attempts by requiring physical device verification beyond password entry. This single control delivers massive risk reduction with minimal operational friction when properly configured.

Password management becomes critical when handling multiple accounts because credential reuse creates cascading vulnerabilities. Dedicated password managers generate and store unique, complex passwords for each profile, eliminating the human memory burden while maintaining security standards. These tools also enable secure credential sharing among team members without exposing passwords through insecure channels like email or messaging apps.
IP address management requires assigning dedicated residential proxies that match account owner locations geographically. LinkedIn tracks login locations and flags suspicious patterns when accounts suddenly access from different countries or data center IP ranges. Using consistent residential IPs maintains natural activity patterns that avoid triggering security alerts during legitimate outreach campaigns.
Access control implementation includes:
- Limiting concurrent sessions to single devices per account
- Auditing access logs weekly to detect anomalies
- Revoking unused API connections and third-party app permissions
- Implementing role-based access for team members
Session and access audits provide early warning systems that catch suspicious activities before they escalate into account compromises. Regular reviews of login histories, device registrations, and API connections identify unauthorized access attempts and misconfigured security settings requiring immediate attention.
Pro Tip: Schedule monthly security training sessions where team members practice identifying phishing emails and review recent LinkedIn policy updates to reduce human error vulnerabilities that technical controls cannot prevent.
Safe automation and outreach strategies
LinkedIn automation success depends on mimicking natural human behavior patterns that avoid detection by platform algorithms. Limiting connection requests to 50-100 per day creates realistic activity volumes that blend with typical user engagement. This disciplined approach sacrifices short-term speed for long-term account sustainability and outreach effectiveness.
IP rotation becomes essential when managing multiple accounts from centralized agency locations. Assigning different residential proxies to each profile prevents LinkedIn from linking accounts through shared IP addresses, which triggers bulk account restrictions. Device fingerprinting adds another layer by varying browser configurations, screen resolutions, and operating systems across profiles to maintain authenticity.
Compliant outreach tools incorporate built-in safeguards that automatically throttle actions, randomize timing intervals, and pause campaigns when detection risks increase. These platforms invest heavily in reverse-engineering LinkedIn's algorithms to keep automation within safe parameters. Choosing tools with proven track records and active development teams reduces ban risks compared to legacy solutions or homegrown scripts.
Safe automation setup follows these steps:
- Configure daily action limits at 60% of known thresholds to maintain safety margins
- Implement 8-12 hour gaps between major automation sessions mimicking work schedules
- Randomize message templates and connection request timing by 15-30 minutes
- Monitor LinkedIn notification emails for security warnings or unusual activity alerts
- Pause all automation immediately upon receiving any platform warnings
Gradual volume ramping protects newly acquired or recently dormant accounts by allowing LinkedIn's trust algorithms to observe consistent, growing activity. Starting at 20-30 daily actions and increasing by 10-15% weekly over two months establishes natural usage patterns. This patience prevents triggering velocity-based detection that flags sudden activity spikes as suspicious automation.
Pro Tip: Maintain detailed logs of daily action counts, response rates, and any platform warnings to identify patterns that predict detection risks before they result in account restrictions.
Advantages of ID-verified LinkedIn accounts
Verified LinkedIn accounts deliver substantial risk reduction compared to fake profiles or rented account alternatives that create liability and operational vulnerabilities. Verified accounts experience 10x fewer restrictions because they carry authentic identity documentation, established activity histories, and natural connection networks that LinkedIn's trust algorithms reward. This verification provides immediate credibility with prospects while reducing the constant threat of sudden bans.
Profile ownership represents a critical distinction because verified accounts function as permanent digital assets agencies can customize, brand, and leverage across years of outreach campaigns. Rented profiles create dependency on third-party providers who maintain control and can revoke access, wipe histories, or increase costs arbitrarily. Full ownership includes email account access, complete profile editing rights, and the ability to build lasting professional networks.
Activity history and connection authenticity matter because LinkedIn evaluates account trustworthiness based on engagement patterns over time. Verified accounts arrive with months of organic activity demonstrating real human usage rather than the hollow shells characteristic of fake profiles. Established connections to genuine professionals provide social proof and network effects that amplify outreach effectiveness.
Verified accounts support sustainable scaling because agencies can confidently invest in profile optimization, content creation, and relationship building without fear of losing access. The benefits of verified LinkedIn accounts extend beyond security to encompass strategic advantages in competitive outreach markets. Building agency reputation on verified foundations creates defensible competitive advantages that compound over time.
Privacy and data protection considerations
Protecting sensitive prospect and client data requires implementing encryption protocols and secure communication channels throughout LinkedIn outreach workflows. LinkedIn Sales Navigator includes role-based access controls and encryption safeguards, but agencies must layer additional protections when exporting data or integrating with CRM systems. End-to-end encryption for stored lead lists, message archives, and contact information prevents unauthorized access during breaches or insider threats.
Role-based access controls limit data exposure by granting team members only the permissions necessary for their specific responsibilities. Junior outreach specialists need different access levels than account managers handling sensitive client communications. This principle of least privilege reduces attack surfaces and contains damage when individual accounts become compromised.
GDPR and CCPA compliance best practices include:
- Obtaining explicit consent before adding prospects to outreach sequences
- Providing clear opt-out mechanisms in every message
- Encrypting all stored personal data at rest and in transit
- Documenting data processing activities and retention policies
- Implementing breach notification procedures with 72-hour response windows
Regular privacy policy updates ensure ongoing compliance as regulations evolve and agency practices change. Transparent communication about data usage builds prospect trust while satisfying legal disclosure requirements. Annual compliance audits identify gaps in data protection protocols before they result in regulatory investigations or penalties.
Client consent statements should explicitly cover LinkedIn data collection methods, storage durations, sharing practices, and security measures. These agreements protect agencies from liability disputes while demonstrating professional data stewardship that differentiates premium service providers. LinkedIn account management privacy protocols become competitive advantages rather than mere compliance burdens.
Implementing LinkedIn security in your agency workflow
Integrating comprehensive security measures into daily agency operations requires systematic implementation following proven change management principles. Begin by auditing current practices to identify security gaps, compliance risks, and workflow inefficiencies that new protocols will address. This baseline assessment provides measurable improvement targets and helps prioritize implementation phases.
Operational integration follows these steps:
- Deploy two-factor authentication across all LinkedIn and email accounts within 48 hours
- Implement password manager with unique credentials for every account by end of week one
- Configure dedicated residential IP proxies matching account owner locations in week two
- Install access monitoring tools and establish weekly audit routines in week three
- Conduct comprehensive team training on new security protocols and compliance requirements
- Document incident response procedures including client notification templates
Employee training must cover LinkedIn policies, phishing recognition techniques, and individual responsibilities for maintaining security hygiene. Interactive workshops where team members practice identifying threats and responding to scenarios build practical skills beyond passive policy acknowledgment. Monthly refresher sessions keep security awareness high as new threats emerge.
Automated alerts reduce response time to suspicious activities by notifying managers immediately when unusual access patterns occur. Configure alerts for login attempts from new locations, password change requests, failed authentication attempts, and LinkedIn security warnings. Real-time notifications enable rapid responses that contain incidents before they escalate.
Incident response planning includes defined roles, communication templates, and escalation procedures that activate during security events. Designate primary and backup security coordinators responsible for investigating alerts, coordinating responses, and communicating with affected clients. Pre-approved messaging templates accelerate transparent client notification while maintaining professional composure during stressful situations.
Pro Tip: Schedule quarterly security audits where external reviewers assess your protocols against current best practices and emerging threats, providing objective feedback that internal teams might miss due to familiarity bias.
Common misconceptions about LinkedIn account security
Myth 1: Two-factor authentication adds unnecessary complexity without meaningful security benefits. Reality: 2FA blocks 99.9% of automated attacks and represents the single most effective security control available. The minor inconvenience of occasional verification codes pales against the devastating impact of account takeovers that disrupt campaigns and damage client relationships.
Myth 2: Fake or rented profiles provide safe, cost-effective alternatives to building authentic accounts. Reality: Fake profiles incur 10x more bans than verified accounts and violate LinkedIn's Terms of Service, creating legal liability. Short-term cost savings evaporate when accounts get permanently restricted mid-campaign, losing all invested effort and prospect relationships.
Myth 3: Aggressive automation scaling does not significantly increase ban risk if using quality tools. Reality: Even sophisticated automation tools cannot fully evade LinkedIn's detection when action volumes exceed natural human patterns. Platform algorithms continuously evolve specifically to identify automation signatures regardless of tool sophistication. Respecting daily limits and mimicking human behavior remains essential for sustained success.
Additional misconceptions include:
- Believing VPNs alone provide sufficient IP protection without residential proxy rotation
- Assuming LinkedIn cannot detect automation through timing pattern analysis
- Thinking compliance requirements only apply to large enterprises, not small agencies
- Expecting deleted LinkedIn data disappears immediately rather than persisting in backups
These false beliefs lead agencies to adopt risky practices that eventually result in account restrictions, compliance violations, or security breaches. Understanding the reality behind common myths enables informed decision-making that balances growth ambitions with sustainable risk management.
Conclusion and next steps for secure LinkedIn outreach
Securing LinkedIn accounts in 2026 requires layered defenses combining technical controls like two-factor authentication and IP management with operational discipline around automation limits and compliance protocols. Verified accounts function as strategic assets that reduce ban risks while supporting sustainable outreach scaling through authentic identity foundations and natural activity patterns. Agencies that integrate comprehensive security frameworks into daily workflows protect client relationships, maintain platform access, and build competitive advantages in increasingly sophisticated threat environments.
The convergence of rising security threats and stricter enforcement makes proactive protection essential rather than optional. Implementing these protocols today prevents tomorrow's crises that disrupt revenue, damage reputations, and consume valuable resources on incident response. Begin by enabling two-factor authentication, auditing current automation practices against safe limits, and evaluating whether verified accounts would strengthen your security posture and outreach effectiveness.
Secure your LinkedIn outreach with BIDVA solutions
Implementing the security and compliance strategies outlined above becomes dramatically simpler when you start with verified LinkedIn accounts designed specifically for agency outreach. BIDVA provides ID verified LinkedIn accounts with authentic identity documentation, established activity histories, and full ownership that eliminate the constant ban risks associated with fake or rented profiles.

Our agency-focused solutions include comprehensive guides for safe LinkedIn account management and proven LinkedIn automation examples that show exactly how to scale outreach while maintaining platform compliance. Each verified account arrives ready for immediate deployment with dedicated IP recommendations, security configuration guidance, and ongoing support to protect your investment.
BIDVA advantages include:
- USA and EU verified accounts with complete identity documentation
- Full profile ownership with email access and customization rights
- Established connection networks and authentic activity histories
- Expert guidance on security protocols and automation best practices
- Ongoing platform policy updates and compliance support
Pro Tip: Combining verified accounts with safe automation tools and comprehensive team training creates synergistic effects where each element reinforces the others, multiplying your outreach effectiveness while minimizing security risks.
What are the most common LinkedIn security threats in 2026?
What are the most common LinkedIn security threats in 2026?
Fake profiles, phishing attacks, account takeover attempts, and automation bans represent the primary security threats facing LinkedIn users in 2026. The platform detected over 86 million fake profiles in early 2024 alone, demonstrating the massive scale of deceptive accounts used to harvest data and conduct social engineering attacks. Data privacy breaches pose additional risks for agencies managing multiple client accounts containing sensitive prospect information.
How does two-factor authentication improve LinkedIn account security?
Two-factor authentication adds a critical verification layer requiring physical device access beyond password knowledge, making unauthorized access 99.9% less likely even when credentials become compromised. This protection proves essential for agencies managing multiple accounts because it prevents automated credential stuffing attacks that exploit password reuse across platforms.
Why should agencies use ID-verified LinkedIn accounts instead of fake or rented profiles?
Verified accounts face 10x fewer platform restrictions than fake profiles because they carry authentic identity documentation and natural activity patterns that LinkedIn's trust algorithms reward. Full profile ownership provides permanent digital assets agencies can customize and leverage across years rather than temporary access vulnerable to provider revocation or sudden policy changes.
What are safe automation limits on LinkedIn to avoid bans?
Keep daily connection requests between 50-100 to mimic natural user behavior patterns that avoid triggering LinkedIn's automated detection systems. Implement IP rotation using residential proxies and vary device fingerprints across accounts to prevent platform algorithms from linking profiles through shared infrastructure that signals bulk automation operations.
Recommended

.png)